ASP offers software solutions developed using state-of-the-art standards, customized towards domestic market. The solutions are intended for use in insurance companies, government institutions, water supply companies, utility billing companies and sports societies.
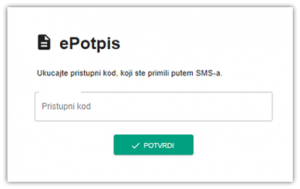
NEWE Signature
Complete solution for electronic signing of documents
 Complete control
Complete control
- Distribution of signed documents
- Sign state tracking of sent documents
- Multi-platform solution
- All personal computer, tablets and mobile devices can be used as receiving and signing devices
- High security
- Access using two-factor authentication (email and mobile phone)
- All communication is completely encrypted
- Simple integration
- Isolated solution that integrates with client envirnoment via services (Restful API)
- Multi-language operation
- Read more >>>
ASP.Ins
Software system supporting non-life insurance business processes
- User authorisation
- Common data
- Business process development
- Sales network
- Strict record keeping
- Insurance sales
- Invoicing
- Billing
- Premium accounting
- Liquidation of claims and recourse processing
- Statistical database
ASP.Revolve
Software system for reinsurance business processes
- User authorization, configuration and internationalization
- Common data – space (zones according to Solvence II, regions, business partners, classifications, coverage type rules)
- Offer – Requests for Offer creation
- Contract – structure creation
- Contract Annex – next year contract renewal, element editing
- Technical part : Accounting digitalisation (TIS), Electronic reception, Automatic analytic division according to contract structure (risk, segment, LOB, COB)
- Active contract accounting
- Passive contract accounting
- Analytical accounting
- Reporting
ASP.Claims
Software system supporting liquidation of claims processes in insurance companies
- Claims filing :
- Place of harmful event – according to state registry of teritorial units and road registry
- Consulting the Motor Vehicle Database (MUP)
- Consulting the Auto Insurance Policy Database
- Claims registration :
- Checking according to the place of harmful event
- Automatic request creation
- Forwarding requests for processing
- Request processing
- Processing – material, non-material (hedonic) damages,
- Recourse processing,
- Court-issued claims,
- Court-issued recourse,
- Enforcement proceedings,
- Claims reactivation
- Claims registry
- Electronic payment
- Analytical accounting
- Transfer to General Ledger
ASP.CRO
Software system for independent registry of deduplicated entities
- The role of CRO is to enable deduplication of persons and legal entities coming from several user application systems
- Microservices communicate with object registry (persons, legal entities, territorial units) and enable asynchronous integration with external systems
- Microservices are integrated with an asynchronous message queue service (Rabbit MQ or similar) for announcement of CRO registry data changes
- Historical object change log (registry supports historical data view for arbitrary date, with change source data)
- Access log for every individual query
- Consolidation identifier linking object duplicates
- “Golden Record” marking – current state of the object (e.g. address)
- During new object entry, a duplicate score is calculated using existing records
 ASP.GuarantyFund
ASP.GuarantyFund
Software system for insurance guaranty funds business processes
- Filing documents and automatic forwarding to organizational units
- Digitalisation (scanning) of input documentation and filing into Document Managament database
- Claim checking using Claims Registry, assigning documents to an already filed request
- Claims filing :
- Place of harmful event – according to state registry of teritorial units and road registry
- Consulting the Motor Vehicle Database (MUP)
- Consulting the Auto Insurance Policy Database
- Claims registration :
- Checking according to the place of harmful event
- Automatic request creation
- Forwarding requests for processing
- Request processing – material, non-material (hedonic) damages, recourse processing, court-issued claims, court-issued recourse, enforcement proceedings, claims reactivation
- Claim transfer to another officer
- Claims processing using obligatory and additional phases and activities
- Creation of template documents in claims processing, filing into DM and e-mailing (electronic claims)
- Electronig communication with all participants
- Creation of pay-off orders and transfer to ebanking
- Creatopm of recourse payment orders
- Automatic entry of orders into analytical accounting
- Automatic connection of payment orders and bank statement items (processing of electronic bank statements)
- Transfer of orders into General Ledger (any software solution)
- Alert system for informing participants of due dates during activities
- Registries of claims, recourse, court and enforcement proceedings
- Registry of complaints
- Reporting to Guaranty Fund, according to regulatory policy
- Integration of all processes into one solution and one database
ASP.Papyrus
Software system for an electronic reception office
- User authorization
- System administration – Organizational structure and employees, Document classification, Document keeping periods, Connection of documents and organizational units, Record keeping, Archive box administration
- Input records – Entry of input documents, scanning, viewing records
- Internal transfer book – Viewing records, Transfer onto employees
- Output records – Entry of output documents, viewing records, postal records creation
- Archive – Candidates for archiving, Archiving documents, viewing records
NEWASP.PrivacyGuard
- Consulting services to ensure compliance with European Union General Data Protection Regulative, domestic legal and normative regulations on personal data and information systems protection, and with Republic of Serbia Personal Data Protection and Information Security Laws.
- Identification of system elements which could be used to access confidential and sensitive data
- Creation of data protection policy, company privacy policy and other information security documentation, as well as safe data management and crisis management procedures
- Creation of Data Protection Impact Assessment analysis and documentation for compliance with GDPR and local legislature
- Personnel education on sensitive and confidential data handling with ZZPL and GDRP compliance
NEWASP.Anonymizer
- Software solution for anonymization of sensitive, confidential and personal data while maintaining database referential integrity and function of applications dependent on anonymized databases
- Software solution for pseudo-anonymization compliant with international standards, normatives and regulations on sensitive, personal, and specially sensitive data protection
- ASP.Anonymizer software solution anonymizes database data in compliance with European Union GDRP and Republic of Serbia Personal Data Protection and Information Security Laws to ensure complete business compliance with domestic and international legislature
- Use of algorithms to detect sensitive and confidential information in compliance with risk assessment of different data categories and domestic, Euroepan and international normative regulations defining confidential and sensitive data categories
- Identification, risk and data hazard assessment of confidential and sensitive data and solution customization to specific client needs and security challenges
NEWASP.Security
- Information security consulting and cyber security risk assessment
- Information security risk and computer system hazard assessment
- Data and computer systems protection consulting for compliance with ISO/IEC 27001:2013 information security international standard
- Security infrastructure and physical security assessment through access control to protected sytems
- Personnel education on cyber security and confidential data protection on computer systems
- Encryption solutions for highly confidential and sensitive data protection
- Encryption and confidential and sensitive data access authorization solutions in compliance with state-of-the-art information security best practices
- Encryption solution based on Kerckhoff’s principle of confidential data protection and Shannon’s theory of cryptographically protected systems
- Cryptoanalytically tested solution for confidential data protection – extremely high resilience to differential and linear cryptoanalytical attacks
- The solution is applicable to systems requiring the highest level of data protection and confidentiality
- Hybrid implementation, layered protection and implementation of hard to detect protected zones
- Compartmentalization of cryptologically protected data and elements of the system
- Possibility to apply confidential data protection from physical attacks onto elements of the system, including personnel coercing
- Software/hardware solutions for information systems protection
- Platform-independent solution implementation (Windows, Linux, Mac OS, BSD)
- Design and implementation of protected information systems
- Construction of protected computers in isolated environment using security hardware and software to obtain a system with high degree of security
- Two-factor user authentication using hardware and software encryption/decryption keys
- Implementation of zone access to confidential data according to security clearance
- Portable device, media and hardware component protection
ASP.Aqua
Software system supporting business processes of water infrastructure companies
- User authorisation
- Common data – Organisation and employees, Classifications, Service, job, water supply and drain price lists, Accounting elements, Interest rates, Fees and taxes
- Registries – Registry of territorial units and house numbers, Registry of persons, Registry of legal entities
- Consumers – Connections, Registration, Deregistration, Meter changing, Metering history
- Auditing – Hodogram, Printing and reading of metering lists, Average consumption, Bill preparation and printing
- Payments and analytical accounting
- Meter servicing
- Work orders
- Third party services
- Reporting